Why MPC Beats TEE for Encrypted Compute
--
The September 2025 attacks didn’t just break Intel SGX. They broke the trust model the on-chain privacy stack quietly built on top of it.
In September 2025, three different academic teams independently demonstrated that Intel SGX, the hardware-level “trusted execution environment” used by some of crypto’s biggest privacy networks, could be broken with under one thousand dollars of equipment.
The attacks have memorable names. WireTap.fail. Battering Ram. SGX.fail (which had already shown the same class of vulnerability back in 2022). Each one demonstrated something slightly different. The common conclusion is the same: hardware-rooted privacy is not the foundation it was sold as.
This matters because a meaningful slice of the on-chain privacy stack (Secret Network, Oasis Sapphire, Phala, Inco Lightning, parts of Nillion) is built on top of TEEs. If the primitive doesn’t hold, neither does the privacy guarantee. And if you are building an application that needs encrypted compute (sealed-bid auctions, private DeFi, confidential AI inference, on-chain salary benchmarks, voting where the count is verifiable but the votes are not), you should care which primitive you bet on.
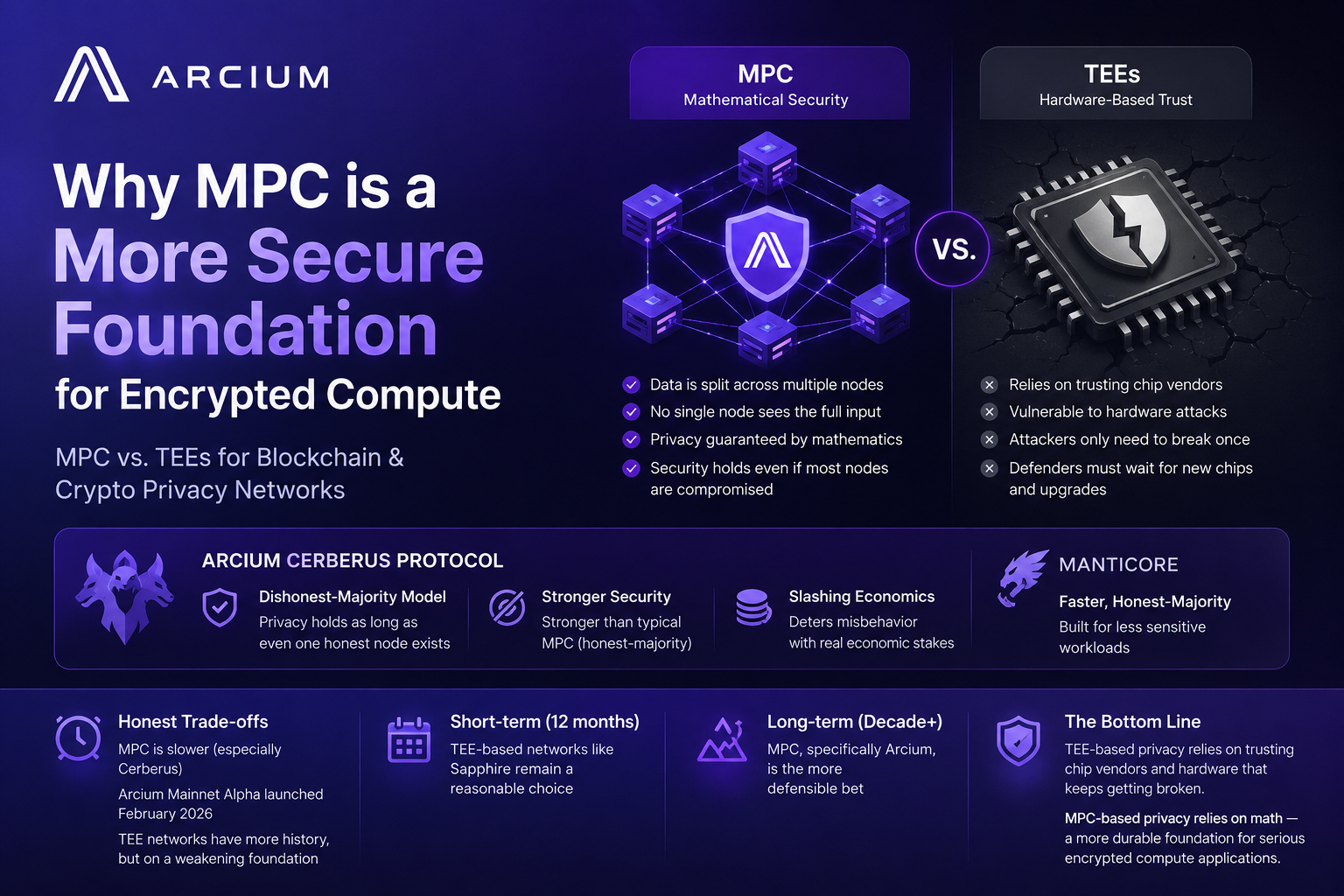
This post is about why MPC (multi-party computation) is structurally a better bet for encrypted compute, and why Arcium’s specific MPC design, Cerberus with its dishonest-majority guarantee, is the most defensible choice available in production today.
The TEE Pitch, and the Problem
A trusted execution environment is, in plain English, a sealed box on a CPU. You put encrypted code and data in. The CPU decrypts inside the box, runs the computation, and gives you back encrypted output. The chip vendor (Intel, AMD, NVIDIA) issues a cryptographic attestation that says yes, this really happened inside the sealed box. If you trust the vendor, you trust the result.
The pitch is seductive. TEEs are fast, sometimes within a few percent of native speed. They support arbitrary computation. They are easier to program than cryptographic alternatives. For years, “encrypted compute” in production effectively meant “TEE-based compute.”
The problem is that the seal turned out to be breakable.
WireTap (September 2025) showed that an attacker with physical access to a server could observe the memory bus, recover SGX attestation keys, and forge attestations, making malicious enclaves indistinguishable from honest ones. Battering Ram extended the work. SGX.fail back in 2022 had already demonstrated that Secret Network’s consensus seed (the master key to every private transaction on the chain) was potentially exposed via xAPIC and MMIO side channels.
The pattern is consistent. Every few years, new research demonstrates a new way to break the seal. Vendors patch. Researchers find another path. Repeat.
To break a TEE-based privacy network, an attacker needs to break the chip a single time. To rebuild trust after a break, defenders need to wait for the next chip generation, hope it doesn’t have similar flaws, convince every operator on the network to upgrade, and accept that the historical state of the network was leaked.
You don’t have to be paranoid to notice the asymmetry. The defender’s job is harder than the attacker’s, and it gets harder over time.
What MPC Does Instead
Multi-party computation takes a different approach. Instead of trusting a sealed box, MPC trusts mathematics.
In an MPC system, your data is split into shares across multiple nodes. No single node ever holds the whole input. The nodes communicate using cryptographic protocols to compute a result, with mathematical guarantees that no individual node ever learns the underlying data. The privacy guarantee comes from math, not from hardware.
This shifts the threat model in an important way. To break MPC privacy, an attacker has to compromise enough nodes to reconstruct the shares. The harder you make that, by requiring more nodes to collude or by tying privacy to even a single honest node, the stronger the guarantee.
This is where Arcium’s design becomes interesting.
Cerberus: One Honest Party Is Enough
Most production MPC systems use what’s called an honest-majority model. As long as more than half the nodes in a committee are honest, privacy holds. This is useful but fragile. Half-honest committees are achievable through reputation, staking, and operator diversity, but they break catastrophically the moment a majority colludes.
Arcium’s Cerberus protocol uses a stronger model: dishonest-majority. Privacy holds as long as one honest node exists. Even if N minus 1 of N nodes collude, including the node performing your computation, your inputs remain hidden.
This is the strongest practical trust assumption available outside of pure zero-knowledge proofs. It does not require a hardware vendor to be honest. It does not require a majority to be honest. It requires exactly one node, anywhere on the network, to refuse to collude.
Combined with the slashing economics built into Arcium’s network (nodes that misbehave lose stake), this gives builders something TEE-based systems structurally cannot offer: a privacy guarantee that does not depend on a single vendor, a single chip, or a single piece of patched firmware.
For workloads where dishonest-majority would be too costly, Arcium also offers Manticore, an honest-but-curious protocol that is faster but trusts the majority. Builders pick which to use per workload. Both run on the same network. The choice is yours, the trade-off is explicit.
The Trade-offs, Honestly
MPC is not free. It is slower than TEE for many workloads. Cerberus’s dishonest-majority guarantee, in particular, costs more rounds of communication than honest-majority alternatives. Not every program is a clean fit.
MPC is also younger as a primitive in encrypted-compute production. Arcium’s Mainnet Alpha launched in February 2026 and is currently in a permissioned phase, with full decentralization scheduled for the Token Generation Event. That is a real caveat. Arcium does not yet have the production track record of Sapphire or Secret.
What it does have is a foundation that adversaries cannot break by spending a thousand dollars on test equipment. The track record of Sapphire and Secret is built on a primitive that academic research has spent the last three years pulling apart. Arcium’s track record is shorter, but the foundation isn’t being pulled apart. It’s being built up.
When you weigh “longer history on a primitive that’s losing ground” against “shorter history on a primitive that’s gaining ground,” the answer depends on how long you expect your application to live. If you are shipping for the next twelve months, Sapphire is a reasonable bet. If you are shipping for the next decade, the calculation looks different.
Why This Matters for Builders
A year ago, the default answer for “where do I deploy encrypted compute?” might reasonably have been Sapphire. Most mature. EVM-compatible. Working bridges. Today, the default is harder to defend. The TEE attacks of 2025 are not a one-off bug, they are the latest entries in a pattern. A network whose privacy guarantee depends on Intel shipping a primitive that adversaries cannot break with sub-thousand-dollar equipment is a network with a structural overhead in its threat model.
Arcium offers a different bet. The privacy guarantee is mathematical. The trust assumption is the strongest one in production MPC. The developer framework (Arcis, Rust-based) is approachable for the Solana ecosystem. The applications it unlocks (Vanish for compliant private trading, Umbra for Solana incognito mode, sealed-bid auctions, confidential matchmaking) depend on a primitive that adversaries cannot break by buying the right chip.
That is a meaningfully different bet than the one TEE-based networks ask you to make. It is also, in 2026, the more defensible one.
If you build encrypted compute, build on a primitive that doesn’t get broken every few years.
For more about Arcium, you can follow and join their official social accounts links below:
https://twitter.com/Arcium
https://discord.com/invite/arcium
Follow me on X:
https://x.com/leosereinn
**Sources:**
- WireTap.fail (Sep 2025) — wiretap.fail
- Battering Ram research (2025)
- SGX.fail (2022) — sgx.fail
- Phala Network’s WireTap response: phala.network/posts/response-to-wiretap-sgx-deprecation
- Secret Network’s WireTap response: scrt.network/blog/secret-network-security-update-intel-sgx-vulnerability-response
- Arcium Mainnet Alpha announcement: arcium.substack.com/p/arcium-mainnet-alpha-is-live
- Arcium Roadmap Update (Sep 2025): arcium.substack.com/p/arcium-roadmap-update