Member-only story
Post-Mortem
We Shipped Broken Auth for Every Guest User — An Azure AD OAuth Post-Mortem
preferred_username was the wrong anchor all along
 Nagaraj6 min read·1 day ago
Nagaraj6 min read·1 day ago--
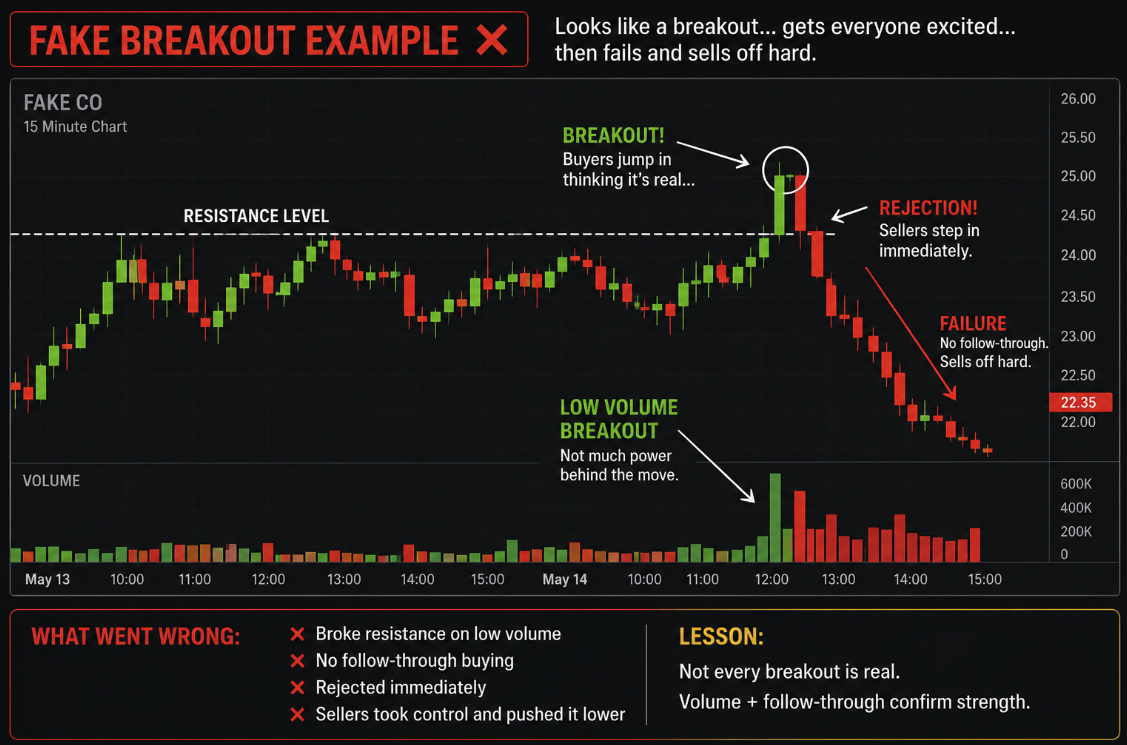
We shipped an Azure AD auth flow that worked for employees but silently failed for every B2B guest user. A post-mortem on preferred_username, oid, and the right way to identify guest users.
The authentication system worked perfectly during quality assurance testing. The internal testers successfully signed in to their accounts which provided them with appropriate access rights to all required information. The project was successfully completed.
A B2B client reported a problem three weeks after launch because their users experienced login difficulties. They successfully logged in but received a 403 error after authentication. The user had an active session and a legitimate Azure AD account but our system identified him with incorrect identity information.
A single claim served as the main problem. The claim functioned as an email address but it did not meet the requirement because it only applied to guest users.