The Centralized Server is a Structural Vulnerability: Why I Built a Zero-Server P2P Node
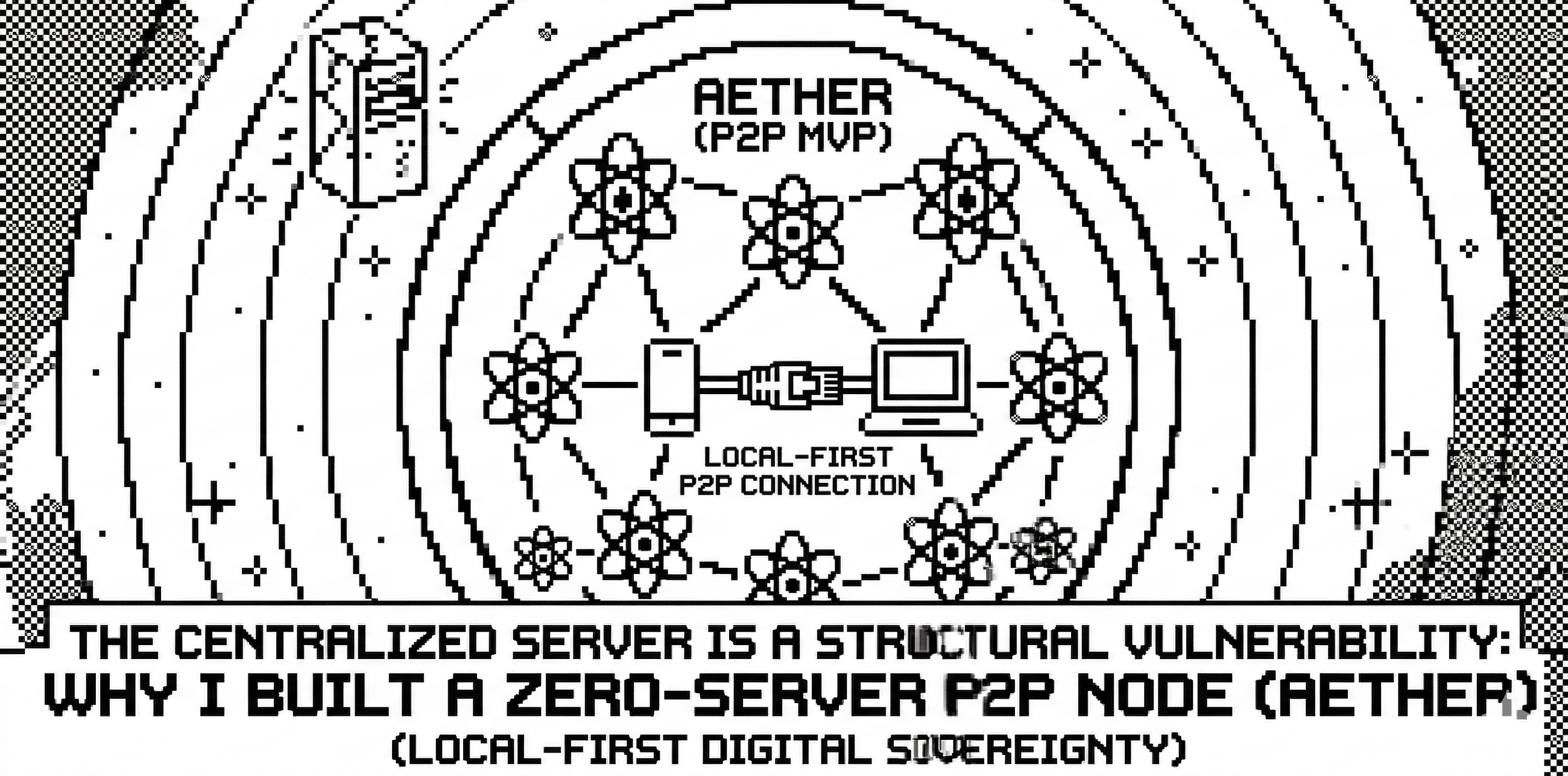
The Core Thesis: Most “secure” messengers today are an architectural illusion. As long as a server sits between you and your recipient — whether for signaling, metadata, or push notifications — your privacy is a matter of corporate goodwill, not a mathematical certainty. I built Aether, a strictly local-first P2P architectural MVP, to prove that digital sovereignty is possible only when we remove the intermediary at the code level.
 Denis Borodin4 min read·Just now
Denis Borodin4 min read·Just now--
I. Philosophy: Identity as Mathematics, Not Permission
The first level of the pyramid is the rejection of the “Account” concept. In a decentralized system, your identity shouldn’t live in a database; it should be the result of an equation.
- Cryptographic Sovereignty (Secp256k1): We abandoned logins and passwords entirely. In Aether, your identity is a key pair. Utilizing the Secp256k1 elliptic curve (the same standard powering Ethereum), the application generates a 32-byte private key locally.
- Addresses vs. Profiles: Your User ID is an Ethereum-format address derived from your key. You don’t ask a server for permission to exist; you exist because the math allows it. This makes the node self-sufficient from the very first millisecond of execution.
II. Security Design: Isolating the Core (Strict IPC)
To build a resilient node, the “brain” must be decoupled from the “face.” We implemented a Strict IPC (Inter-Process Communication) pattern to mitigate the risks inherent in desktop web environments.
- The Dumb UI (Renderer): The React frontend is a pure presentation layer. It has zero knowledge of cryptographic keys and no direct access to the networking stack.
- The Main Process (The Vault): All
libp2plogic and key management live in the isolated Electron Main process. - The Secure Bridge: Communication happens via
contextBridge. Even if the UI is compromised via an XSS attack, the attacker cannot "reach out" to the network or extract keys—they are physically inaccessible to the frontend environment.
III. Tactical Engineering: Solving the P2P Bottlenecks
Moving away from the cloud forces an engineer to solve problems usually delegated to AWS or Google.
- Escaping ESM Dependency Hell: Modern P2P libraries are pure ES Modules, which often clash with Electron’s ecosystem. We resolved this with a custom Vite configuration that bundles
@libp2pdependencies directly into the Main process, ensuring a stable, monolithic execution environment. - Discovery via mDNS: To achieve a zero-server setup, we utilized Multicast DNS. Nodes broadcast their presence on the local network. The moment you open Aether, you “see” peers via physical proximity, not via a central directory.
- Noise Protocol Encryption: Every data stream is wrapped in the Noise Protocol framework. To any external observer, your communication is indistinguishable from cryptographic noise.
IV. The Roadmap: From Local MVP to Mesh Network
An MVP is a baseline, not a destination. To move from a prototype to a production-ready autonomous node, we are migrating toward:
- Global Discovery (Kademlia DHT): Moving beyond LAN to find peers across the internet using bootstrap nodes and Distributed Hash Tables.
- Perfect Forward Secrecy (Double Ratchet): Implementing the Signal-style Double Ratchet algorithm to ensure that even if a session key is compromised, past messages remain encrypted.
- Local Persistence (SQLite): Embedding history directly into the node, ensuring that your data never sees a cloud backup.
The “So What”: Why a 21-Year-Old Growth Lead is Building This
As a Growth Lead and former Data Lead, my professional life revolves around “The Machine.” I build the algorithms that scrape open-source data, analyze behavioral patterns, and turn human interactions into “leads.” I know exactly how easy it is to deanonymize a user through metadata alone.
The “Cloud” is just someone else’s computer, and right now, that computer is watching you.
I believe we aren’t on Mars yet partly because the brightest engineering minds of my generation are trapped optimizing ad-click conversions for $0.01. I am 21, and I don’t want my legacy to be “higher retention rates.”
Aether is an exploration of a different path — one where technology serves the autonomous individual, not the centralized aggregator.
The code is open. The future is peer-to-peer.
[GitHub Repository] | [HackerNoon] | [LinkedIn]