Navigating the Tension: Privacy vs AML in Australia
 Purva Buch4 min read·Just now
Purva Buch4 min read·Just now--
Privacy vs AML in Australia: In a Nutshell
Australian firms, tranche 1 and tranche 2, both face a structural conflict between privacy and AML obligations:
- AML/CTF laws require long-term data retention and secrecy
- Privacy laws (APP 11.2) require data minimisation and timely destruction
- Tipping-off rules restrict transparency and breach notification
- Systems must isolate, retain, and delete data simultaneously
This is not just a legal issue; it is a system design challenge.
Introduction to AML-Privacy Paradox
Australian reporting entities face a structural paradox: the anti-money laundering (AML) framework demands exhaustive data collection, persistent retention, and operational secrecy, while the Privacy Act 1988 mandates strict data minimisation, transparency, and timely destruction. This is not merely a policy conflict; it is a system-level engineering challenge. Firms must architect data environments that reconcile the persistent auditability required to track illicit financial flows with the privacy-by-design imperative to continuously purge sensitive personal information.
Why Privacy and AML Obligations Diverge in Australia
The divergence is rooted in competing regulatory objectives. Privacy frameworks empower the individual, requiring open and transparent management of personal information (APP 1) and granting rights to access and correct data. Conversely, AML frameworks prioritise financial system integrity, leveraging secrecy to prevent the disruption of investigations.
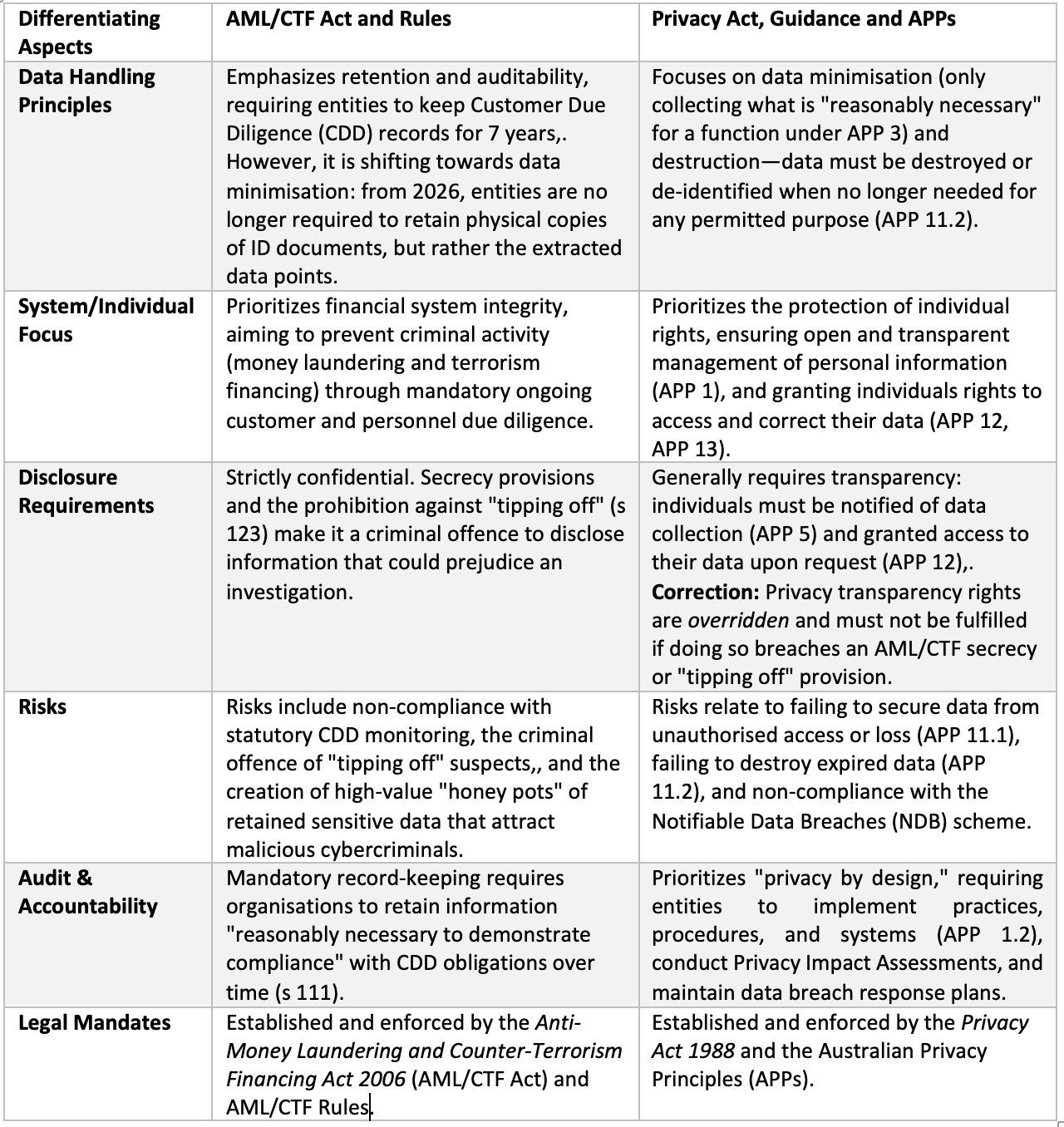
The table below highlights key points of distinction between AML and Privacy obligations in the context of handling information.
These obligations are not just legally different, they require fundamentally different system behaviour.
AML enforcement requires secrecy, structurally overriding privacy transparency and data access rights. Under the AML/CTF Act, reporting entities are prohibited from notifying individuals of a data breach if doing so would reveal “AUSTRAC information” or constitute “tipping off”.
OAIC Privacy Expectations on Retention and Destruction
The Office of the Australian Information Commissioner (OAIC) — Privacy guidance for reporting entities under the AML/CTF Act strictly enforces Australian Privacy Principle (APP) 11.2, requiring entities to take reasonable steps to destroy or de-identify personal information once it is no longer needed for any permitted purpose. Retaining vast repositories of identification documents indefinitely is no longer acceptable. Prolonged retention of sensitive customer due diligence data creates honeypots that attract cybercriminals. To mitigate these cyber risks, the OAIC expects firms to actively manage data lifecycles and forcefully limit their holdings.
AML/CTF Record-Keeping Requirements
Conversely, the AML/CTF Act enforces mandatory record-keeping periods to ensure persistent auditability. Reporting entities are legally authorised to retain records of customer due diligence (CDD) to demonstrate compliance. For legacy records, this means retaining information for seven years following the end of a business relationship or the last occasional transaction. Statutory AML retention mandates systematically limit the immediate application of privacy data destruction requirements. However, from 31 March 2026 (for Tranche 1) and 1 July 2026 (for Tranche 2), entities will no longer be required to retain scanned copies or photocopies of physical identity documents.
Where the Tension Becomes Operational
This friction materialises directly within IT architecture and operational workflows:
- Retention vs destruction: Firms must execute a targeted extraction process during onboarding. Instead of hoarding physical document scans, systems must capture isolated data points (name, expiry date, document number) and the verification outcome, while automatically purging the underlying image files. The transition from retaining document images to isolated data points shifts AML record-keeping toward data-minimisation.
- De-identification vs auditability: While privacy laws encourage de-identification to reduce risk, AML obligations demand that reporting entities maintain identifiable records to trace financial activity and conduct ongoing CDD. Furthermore, handling data subject access requests requires a silent screening layer to avoid tipping off suspects. Secrecy and tipping-off provisions in AML frameworks structurally suppress data subject breach notification rights.
Interpreting “Reasonable Steps” in AML Contexts
The OAIC acknowledges the sheer complexity of retrofitting legacy systems to immediately purge historical ID copies. In this context, “reasonable steps” under APP 11.2 allows for transitional pragmatism. If immediate deletion of legacy scans is technically unfeasible, firms must actively isolate this data. Regulators demand firms implement technical measures to put historical AML data beyond use pending destruction. This requires strictly limiting access, applying robust technical security, and committing to future deletion through a documented, management-approved transition plan.
Why Standard Compliance Frameworks Fail
Generic privacy overlays cannot accommodate the rigidity of AML rules. Standard enterprise policies often default to blanket retention or aggressive deletion without mapping the specific statutory trigger for each data asset. Generic automated deletion schedules fail when balancing continuous AML monitoring against rigid privacy destruction mandates. To survive regulatory scrutiny, firms must deploy dynamic retention schedules and personal information inventories that recognise exactly when a specific AML legal exception expires, immediately triggering APP 11.2 privacy destruction protocols.
Conclusion: Same Law, Different System Behaviour
Australian reporting entities cannot rely on static compliance manuals to bridge the gap between privacy and AML obligations. Operational alignment requires granular data mapping, sophisticated identity verification pipelines, and automated disposal mechanisms. True compliance requires architecting systems that mathematically isolate data while satisfying competing regulatory retention timelines. Only by embedding these conflicting rules directly into system logic can firms successfully manage both financial crime risk and data privacy.
For more short, structured insights on how compliance frameworks translate into real system design, you can follow my work on LinkedIn.